New Approach Based on Homomorphic Encryption to Secure Medical Images in Cloud Computing
DOI:
https://doi.org/10.48048/tis.2022.3970Keywords:
Cloud computing, Medical image processing, Homomorphic encryption, MapReduce, Hadoop framework, BA algorithmAbstract
In recent years, there has been a growing demand for the adoption of cloud in healthcare to process medical data. Unfortunately, this emerging new paradigm faces several challenges, as customer data is stored on remote servers rather than on premise solutions. This is considered to be the main root cause of the major security vulnerabilities encountered in outsourced calculations. Indeed, to solve this problem we used encryption; customers should encode their sensitive data when considering adopting cloud services. One of the biggest challenges is establishing controls that completely protect secret data from insider attacks, while also supporting the computations. In addition, applying complex encryption schemes can have a negative effect on system performance.
This study focuses in particular on homomorphic techniques and their main applications, as well as their limitations. Unlike traditional encryption methods, homomorphic schemes are used not only to reduce the security risks associated with cloud technology, but also to process cipher texts. However, current efforts in this area need to be further developed to strike the right balance between privacy risks and data utility. In this regard, we offer a hybrid approach that offers the possibility of quickly processing health records in a secure manner. Our main contribution is the proposal of a new method based on Hadoop MapReduce functions in conjunction with a multi-agent system to maintain data confidentiality. In addition, and to design intelligent distributed computing for efficient management of Virtual Machine (VM) workloads, we used a method based on the Bat Algorithm (BA).
HIGHLIGHTS
- This article is about a system based on homomorphic encryption to secure medical images stored in cloud computing
- Its objective is to reduce the security risks associated with cloud technology, but also to process ciphertexts
- This system is based on the MapReduce function to benefit from parallelism during data processing and the Hadoop framework to develop and implement secure medical image processing applications in the cloud
- Hadoop and MapReduce are in conjunction with a multi-agent system to perform distributed data processing
- Our system uses a method based on the Bat (BA) algorithm to ensure efficient management of the workload of virtual machines (VMs) and thus guarantee load balancing
GRAPHICAL ABSTRACT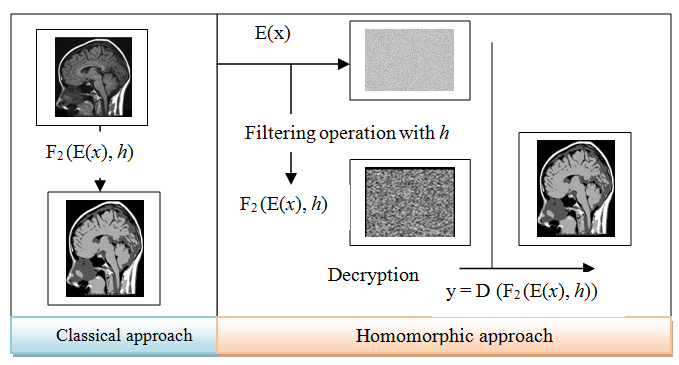
Downloads
References
R Parks, RT Wigand, MB Othmani, Z Serhier and O Bouhaddou. Electronic health records implementation in Morocco: Challenges of silo efforts and recommendations for improvements. Int. J. Med. Inform. 2019; 129, 430-7.
S Tanwar, K Parekha and R Evans. Blockchain-based electronic healthcare record system for healthcare 4.0 applications. J. Inform. Secur. Appl. 2020; 50, 102407.
J Haskew, G Ro, K Saito, K Turner, G Odhiambo, A Wamae, S Sharif and T Sugshita. Implementation of a cloud-based electronic medical record for maternal and child health in rural Kenya. Int. J. Med. Inform. 2015; 84, 349-54.
HN Moulick and M Ghosh. Medical image processing using a service oriented architecture and distributed environment. Am. J. Eng. Res. 2013; 2, 52-62.
F Farokhi, I Shames and N Batterham. Secure and private cloud-based control using semi-homomorphic encryption. IFAC-PapersOnLine 2016; 49, 163-8.
AM Vengadapurvaja, G Nisha, R Aarthy and N Sasikaladevi. An efficient homomorphic medical image encryption algorithm for cloud storage security. Proc. Comput. Sci. 2017; 115, 643-50.
A Lathey and PK Atrey. Image enhancement in encrypted domain over cloud. ACM Trans. Multimed. Comput. Comm. Appl. 2015; 11, 38
M Mohanty, WT Ooi and PK Atrey. Secret sharing approach for securing cloud-based pre-classification volume ray-casting. Multimed. Tools Appl. 2016; 75, 6207-35.
P Singh, B Raman, N Agarwal and PK Atrey. Secure cloud-based image tampering detection and localization using POB number system. ACM Trans. Multimed. Comput. Comm. Appl. 2017; 13, 23.
M Marwan, A Kartit and H Ouahmane. A cloud-based framework to secure medical image processing. J. Mobile Multimed. 2018; 14, 319-44.
M Marwan, A Kartit and H Ouahmane. A cloud-based solution for collaborative and secure sharing of medical data. Int. J. Enterprise Inform. Syst. 2018; 14, 128-45.
X Yi, R Paulet and E Bertino. Homomorphic encryption and applications. Springer, Cham, Switzerland, 2014.
MM Potey, CA Dhote and DH Sharma. Homomorphic encryption for security of cloud data. Proc. Comput. Sci. 2016; 79, 175-81.
M Marwan, A Kartit and H Ouahmane. Applying homomorphic encryption for securing cloud database. In: Proceedings of the 4th IEEE International Colloquium on Information Science and Technology, Tangier, Morocco. 2016, p. 658-64.
P Paillier. Public-key cryptosystems based on composite degree residuosity classes. In: J Stern (Ed.). Advances in cryptology - EUROCRYPT’99. Lecture notes in computer science. Vol 1592. Springer, Heidelberg, Germany, 1999, p. 223-38.
RL Rivest, A Shamir and L Adleman. A method for obtaining digital signatures and public-key cryptosystems. Comm. ACM 1987; 21, 120-6.
P Martins, L Sousa and A Mariano. A survey on fully homomorphic encryption: An engineering perspective. ACM Comput. Surv. 2018; 50, 83.
C Gentry. 2009, A fully homomorphic encryption scheme. Ph. D. Dissertation. Stanford University, California, United States.
MV Dijk, C Gentry, S Halevi and V Vaikuntanathan. Fully homomorphic encryption over the integers. In: H Gilbert (Ed.). Advances in cryptology - EUROCRYPT 2010. Lecture notes in computer science. Vol 6110. Springer, Heidelberg, Germany, 2010.
VS Gorti and U Garimella. An efficient secure message transmission in mobile ad hoc networks using enhanced homomorphic encryption scheme. Global J. Comput. Sci. Tech. Netw. Web Secur. 2013; 13, 20-33.
RK Challa, J Kakinada, GV Kumari and B Sunny. Secure image processing using LWE based homomorphic encryption. In: Proceedings of the 2015 IEEE International Conference on Electrical, Computer and Communication Technologies, Coimbatore, India. 2015, p. 1-6.
M Gomathisankaran, X Yuan and P Kamongi. Ensure privacy and security in the process of medical image analysis. In: Proceedings of the 2013 IEEE International Conference on Granular Computing, Beijing, China. 2013, p. 120-5.
SR Kanithi and AG Latha. Secure image processing using discrete wavelet transform and paillier cryptosystem. Int. J. Mag. Eng. Tech. Manag. Res. 2015; 2, 1270-6.
N Habeep and RD Raj. Homomorphic encrypted domain with DWT methods. Int. J. Inventions Comput. Sci. Eng. 2014; 1, 2348-3431.
P Yang, X Gui, J An and F Tian. An efficient secret key homomorphic encryption used in image processing service. Secur. Comm. Netw. 2017; 2017, 7695751.
S Farah, MY Javed, A Shamim and T Nawaz. An experimental study on performance evaluation of asymmetric encryption algorithms. Recent Adv. Inform. Sci. 2012; 8, 121-4.
SJA Nair and TRG Nair. VM placement with effective energy management in cloud using optimal VM allocation framework (OVAF). Indonesian J. Electr. Eng. Comput. Sci. 2020; 18, 1531-8.
WARWM Isa, AIH Suhaimi, N Noordin, AF Harun, J Ismail and RA Teh. The factors influencing cloud computing adoption in higher education institution. Indonesian J. Electr. Eng. Comput. Sci. 2020; 17, 412-9.
S Deshpande and R Ingle. Preferences based customized trust model for assessment of cloud services. International Journal of Electrical and Computer Engineering. 2018; 8, 304-25.
J Mahdjoub, Z Guessoum, F Michel and M Herbin. A multi-agent approach for the edge detection in image processings. In: Proceedings of the 4th European Workshop on Multi-Agent System, Lisbon, Portugal. 2006.
FDL Prieta, S Rodríguez, P Chamoso, JM Corchado and J Bajo. Survey of agent-based cloud computing applications. Future Generat. Comput. Syst. 2019; 100, 223-36.
SM Banaei and HK Moghaddam. Hadoop and its role in modern image processing. Open J. Mar. Sci. 2014; 4, 239-45.
MH Almeer. Cloud hadoop map reduce for remote sensing image analysis. J. Emerg. Trends Comput. Inform. Sci. 2012; 3, 637-44.
S Arietta, J Lawrence, L Liu and C Sweeney. Hipi-hadoop image processing interface, Available at: http://hipi.cs.virginia.edu/about.html, accessed January 2020.
A Ullah, NM Nawi, J Uddin, S Baseer and AH Rashed. Artificial bee colony algorithm used for load balancing in cloud computing: Review. IAES Int. J. Artif. Intell. 2019; 8, 156-67.
XS Yang. A new metaheuristic bat-inspired algorithm. In: Proceedings of the Nature Inspired Cooperative Strategies for Optimization, Heidelberg, Germany. 2010.
M Adhikari, S Nandy and T Amgoth. Meta heuristic-based task deployment mechanism for load balancing in IaaS cloud. J. Netw. Comput. Appl. 2019; 128, 64-77.
Downloads
Published
How to Cite
Issue
Section
License

This work is licensed under a Creative Commons Attribution-NonCommercial-NoDerivatives 4.0 International License.